Hands-On Cybersecurity Implementation
We specialize in the implementation and operational management of robust cybersecurity solutions, helping you safeguard data, fortify systems, and build a resilient security posture against evolving threats.
Comprehensive Cybersecurity Implementation Services.
We provide hands-on execution and implementation across the full spectrum of cybersecurity domains to actively protect your digital assets.
Identity & Access Management Execution:
Implementation of SSO, MFA, and Adaptive Authentication, Privileged Access Management (PAM) deployment, Directory integration and identity federation.
SOC & Threat Monitoring:
Setup and operation of SIEM platforms, Threat detection and alert triaging, SOAR playbook implementation for automated response, Log ingestion, correlation rules tuning, and dashboarding.
Penetration Testing Execution:
Exploiting identified vulnerabilities across applications, networks, and infrastructure, Social engineering simulation campaigns, Blue teaming for detection tuning and response testing.
Vulnerability Management & Remediation:
Scheduling and running internal/external vulnerability scans, Manual validation and risk-based remediation planning, Patch management automation and configuration hardening.
Data Protection & DLP Implementation:
DLP policy design and enforcement across endpoints, network, and cloud, Implementation of encryption and secure file sharing, Email security implementation.
Cloud Security Implementation:
Cloud Security Posture Management setup for AWS, Azure, and GCP, Cloud Workload Protection, firewall rules, and IAM hardening, Configuration of CASB for SaaS protection, Encryption, key management, and logging configuration.
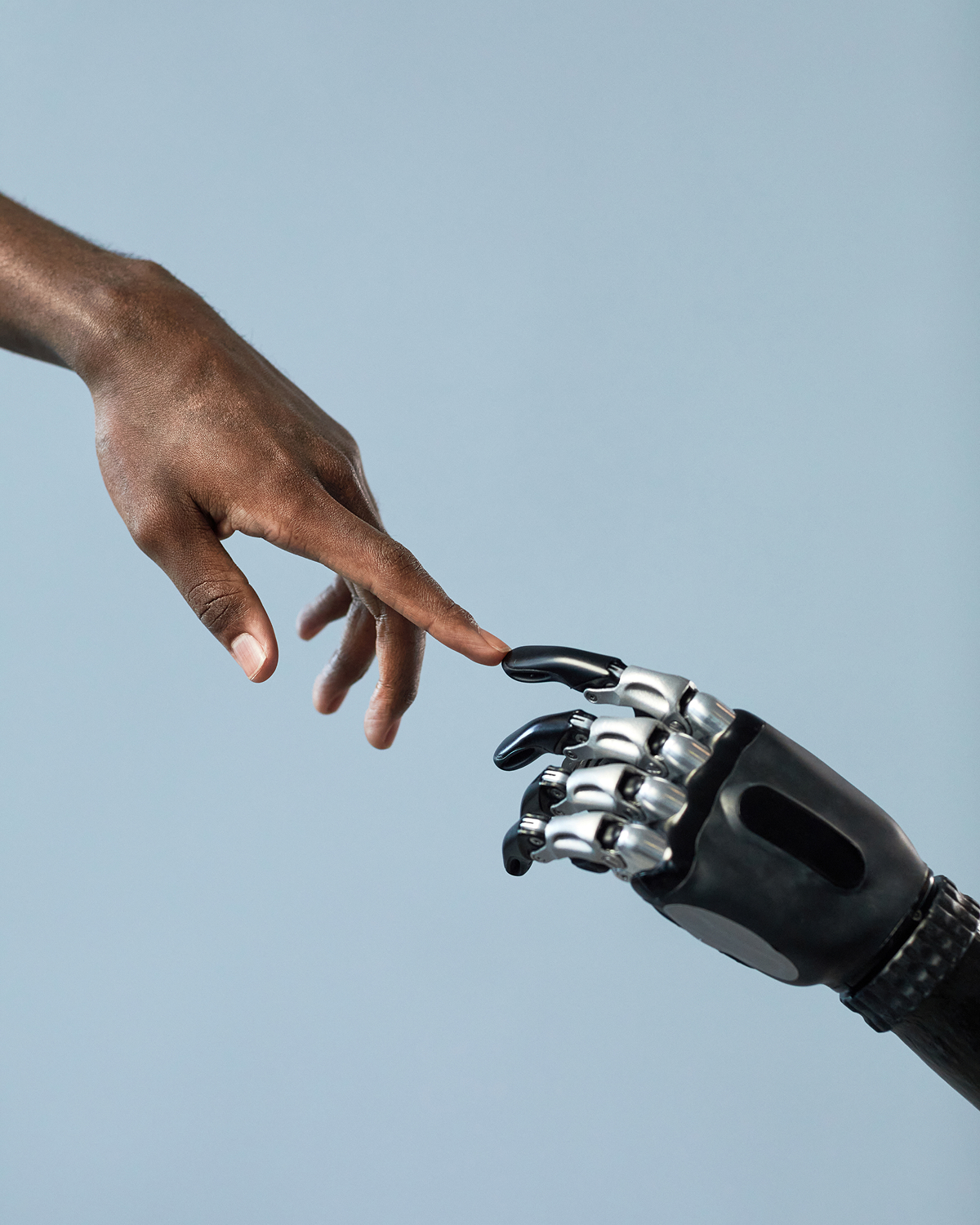
Your Partner in Proactive Defense Implementation.
Choosing the right implementation partner is critical for a strong security posture. SysMind offers a unique combination of expertise, focus, and agility.
Our Technology Ecosystem
Our deep, hands-on expertise across a broad ecosystem of modern technologies allows us to architect, develop, and manage robust, scalable solutions that drive tangible business outcomes.








Holistic Solutions for a Secure Enterprise.
Our cybersecurity expertise is a core component of our broader technology implementation services, designed to build a secure and efficient enterprise.